How to Cut SaaS DDoS Downtime to Seconds with Flowtriq
DDoS isn’t a security problem—it’s a P&L problem. Flowtriq treats it that way.
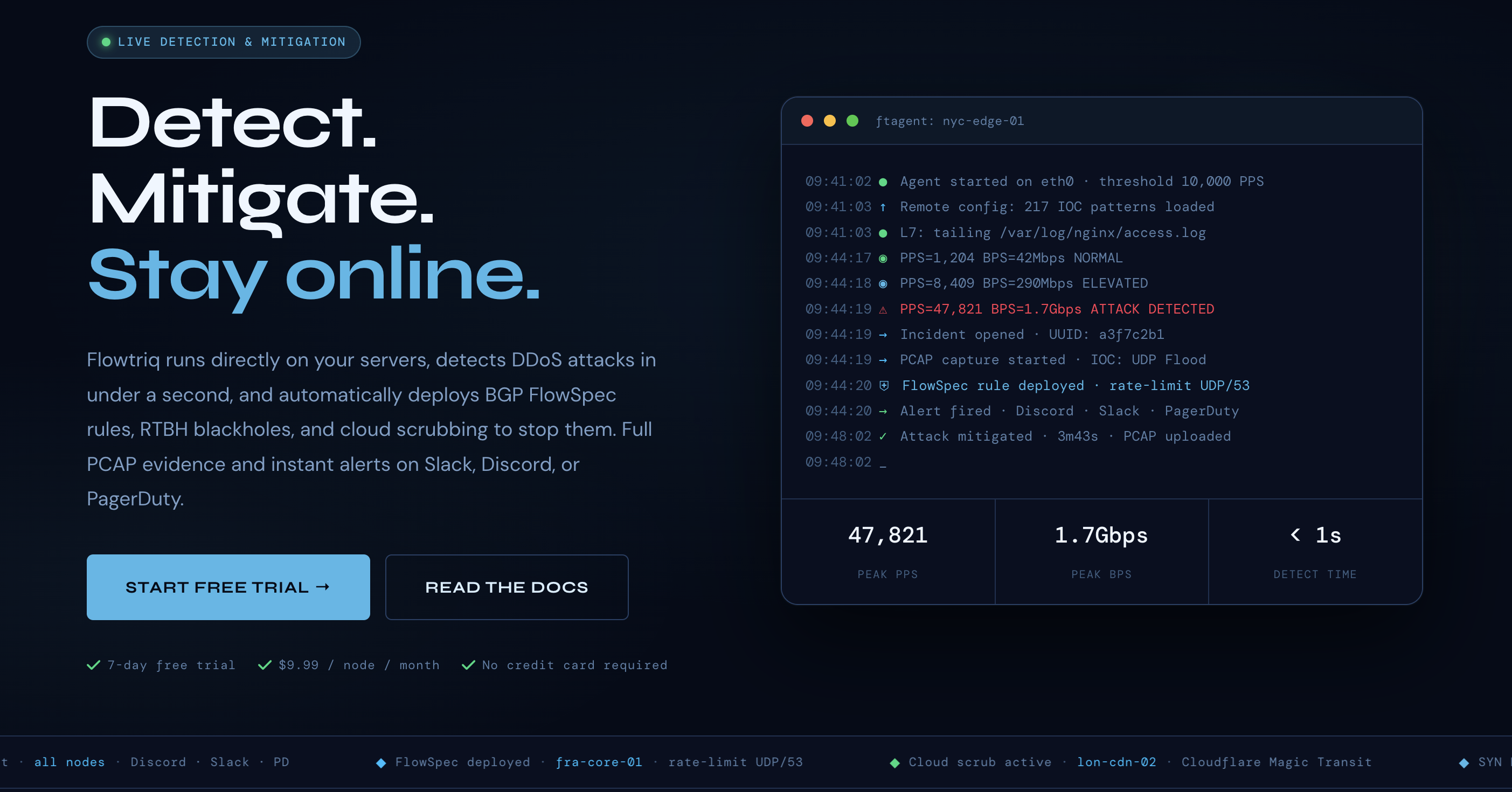
Most “DDoS protection” buys you a SOC alert and a long bridge call. Flowtriq flips the script: a lightweight Linux agent learns your baseline, detects anomalies sub-second, and auto-mitigates before customers feel it. For SaaS leaders, the bottom line is simple—convert unpredictable downtime into predictable cost with $9.99/node/month pricing and response in under one second. Vibe check: this is one of our Easy Setup Tools that feels like a Weekend Project, not a re-architecture.
The Business Case
The economic case hinges on compressing MTTD/MTTR from minutes to seconds and stabilizing OpEx. Industry data pegs downtime at $300K+ per hour for most enterprises, with many exceeding $1M/hour (ITIC 2023). DDoS remains a top cause of availability incidents across SaaS and gaming, with volumetric and multi-vector attacks rising in frequency and complexity (Cloudflare DDoS Threat Reports; NETSCOUT Threat Intelligence).
Model the impact: assume a mid-market SaaS runs 40 production-facing nodes and experiences two DDoS incidents per quarter at 12 minutes effective impact each. At $300K/hour, that’s ~$120K/quarter in direct productivity and revenue loss, excluding churn and SLA credits. Flowtriq’s agent-based detection and automated mitigation (FlowSpec/RTBH/scrubbing) aim to cut effective impact from double-digit minutes to seconds, while its flat $9.99/node/month eliminates traffic-based overages common with cloud scrubbing. Annualized, 40 nodes cost ~$3,840; preventing a single 12-minute event can pay for the platform multiple times. Add the forensic value of triggered PCAPs and an immutable audit log—useful for post-incident root cause, compliance, and contractual defense.
Key Strategic Benefits
-
Operational Efficiency:
- Sub-second anomaly detection with auto-deployed mitigations removes human-in-the-loop delays and shrinks bridge calls. Multi-channel alerts (Slack, PagerDuty, Discord, SMS, webhooks) fire within one second, aligning responders only when escalation is warranted. Automated runbooks convert tribal knowledge into repeatable playbooks.
-
Cost Impact:
- Flat, per-node pricing (no traffic or per-alert surcharges) stabilizes budgets even during high-variance attack windows. By cutting downtime minutes and SLA payouts, leaders can reallocate spend from reactive scrubbing to proactive resilience—often a net reduction in total cost of availability.
-
Scalability:
- The agent deploys in under two minutes on any Linux host and manages multi-node fleets from a single dashboard—suited to SaaS footprints that scale horizontally. Dynamic baselining adapts thresholds per node, preserving protection as traffic patterns evolve (seasonality, feature launches, geo-expansion).
-
Risk Factors:
- Agent dependence means Linux coverage is strong but non-Linux edges need alternate controls. False positives on edge cases (e.g., unusual product launches) require careful baseline warm-up and sensible escalation tiers. FlowSpec/RTBH require router support and safe-guardrails to avoid self-inflicted blackholes; governance over automated changes is essential.
Implementation Considerations
Expect a rapid pilot-to-prod path. The ftagent installs via Python on Linux in under two minutes per node; most teams can pilot on 3–5 representative nodes in a day. Integration touchpoints: network devices supporting BGP FlowSpec and RTBH, plus optional cloud scrubbing connectors (Cloudflare Magic Transit, OVH VAC, Hetzner). Configure escalation policies that sequence mitigations from least to most disruptive, and enable automatic PCAP capture for every event.
Change management is light but deliberate: define ownership (SRE or NetSec), codify runbooks, and route alerts to existing on-call frameworks (PagerDuty/Opsgenie). Security requires least-privilege credentials for network automation and audit review of the immutable action log. For enterprise rollouts (50+ nodes), plan for custom IOC libraries and extended 365-day PCAP retention. Baseline learning should precede high-traffic launches; simulate attacks in a controlled window to validate playbooks. This is squarely in our Chill Picks: an Easy Setup Tool that most teams can stand up as a Weekend Project.
Competitive Landscape
Flowtriq’s differentiation is agent-first, packet-level detection with sub-second action and flat pricing. Cloud-first scrubbing options such as Cloudflare Magic Transit (https://www.cloudflare.com/magic-transit/), Akamai Prolexic (https://www.akamai.com/products/prolexic), and AWS Shield Advanced (https://aws.amazon.com/shield/advanced/) deliver massive network capacity and managed response but often add per-traffic or per-GB economics, with detection/engagement sometimes gated by thresholds. Hardware-centric solutions like Radware DefensePro (https://www.radware.com/products/defensepro/) and NETSCOUT Arbor (https://www.netscout.com/arbor/ddos-protection) excel at carrier/ISP scale but require appliance deployment and capital spend.
For third-party comparisons, see G2’s DDoS Protection category (https://www.g2.com/categories/ddos-protection) and Forrester’s DDoS Mitigation Wave (https://www.forrester.com/report/the-forrester-wave-ddos-mitigation-solutions-q1-2021/RES166921). Flowtriq also signals credibility with original research (e.g., Mirai botnet kill switch CVE-2024-45163: https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2024-45163) and a public State of DDoS 2026 report, plus threat intel correlation across 642K+ IOCs.
Recommendation
Adopt a phased pilot. In week one, deploy Flowtriq on 5 high-risk nodes, enable alerting, and configure a three-tier mitigation runbook (rate-limit → FlowSpec → RTBH/scrub). In week two, run a red-team volumetric simulation after baseline learning and review PCAP/audit logs. If effective impact stays sub-minute with no critical false positives, expand to all production nodes and formalize governance. Lock in annual pricing per node, and retain existing scrubbing as a final-tier fallback for peak events.